CYBERSECURITY SERVICES
Comprehensive security solutions powered by Fortinet Security Fabric and leading global vendors
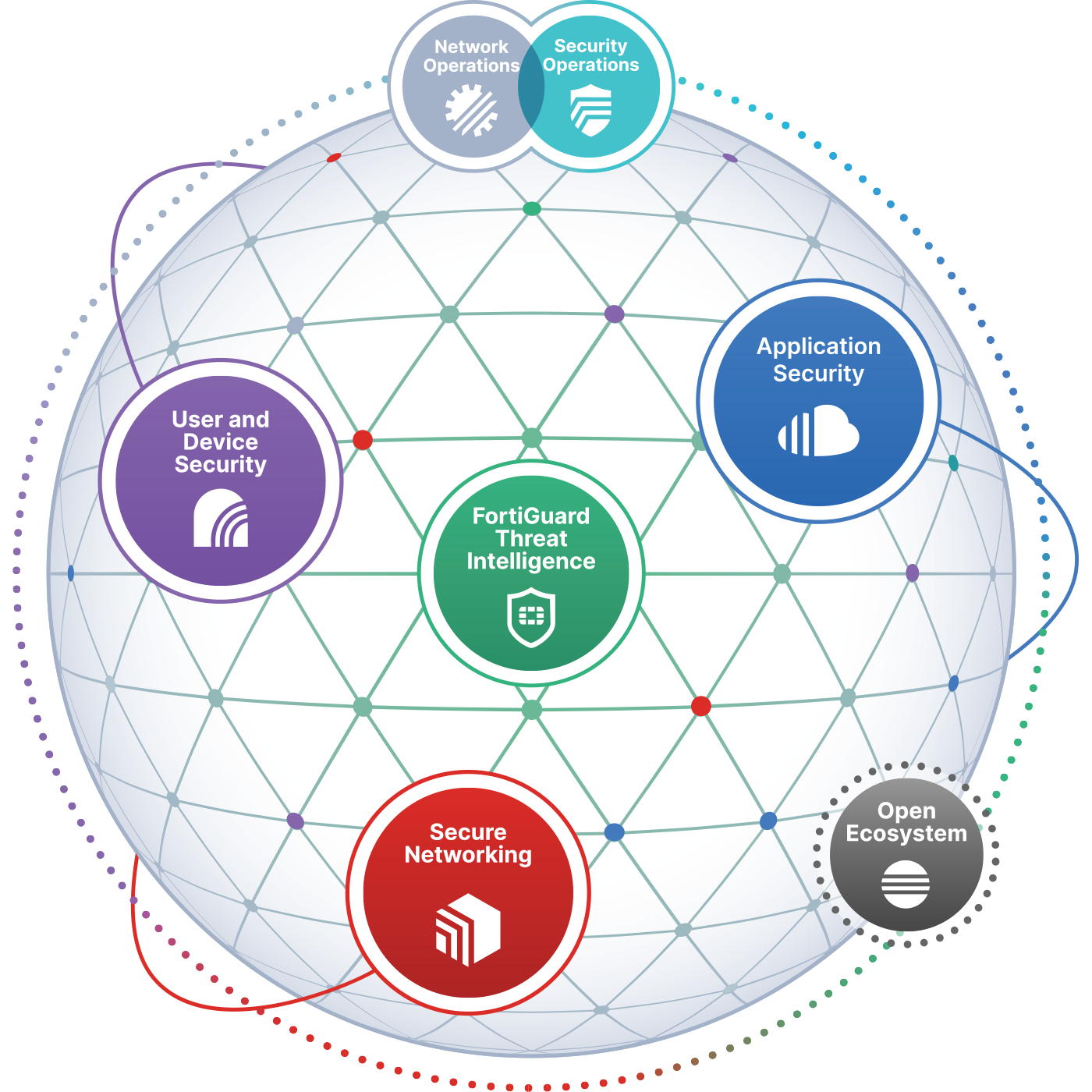
Fortinet Security Fabric
The industry's only integrated, automated, and intelligence-driven security platform covering your entire digital attack surface

Kaspersky Security
- Endpoint Security
- Hybrid Cloud Security
- Threat Intelligence
- EDR & XDR Solutions

Trend Micro
- Cloud One Platform
- Deep Security
- Vision One XDR
- Email & Web Security

Sophos Security
- Intercept X Endpoint
- XG Firewall
- Email Security
- Synchronized Security
Everything You Need to Know About Cybersecurity in Saudi Arabia
Saudi Arabia is becoming one of the most digitally advanced markets in the region, which makes cybersecurity a top priority for every organization. With increasing threats, strict national regulations, and rapid digital transformation, businesses must ensure their systems, data, and operations are fully protected. Cybersecurity in the Kingdom focuses on strong compliance with frameworks like NCA ECC, SAMA Cybersecurity Framework, and CITC cloud regulations—along with modern defenses for IT, OT, and cloud environments. Understanding these requirements and implementing the right controls helps companies reduce risk, maintain business continuity, and build a secure foundation for future growth across the Saudi market.
Saudi Arabia is a rapidly growing digital economy, and cyber-attacks are increasing across all sectors. Strong cybersecurity is essential to protect data, ensure business continuity, and meet national regulatory requirements.
Depending on your sector, you may need to comply with NCA (National Cybersecurity Authority) controls, SAMA Cybersecurity Framework, CITC cloud regulations, or sector-specific requirements (energy, healthcare, finance, etc.).
A professional security assessment identifies gaps, compliance risks, and missing controls. Prime Links provides a complete assessment aligned with Saudi regulatory standards.
IT security protects business systems and data. OT security protects industrial systems like SCADA, PLCs, and critical infrastructure. Both require different tools and approaches.
Yes. SMBs are frequently targeted because they often have weaker defenses. Basic protection can prevent major financial and operational losses.
Ransomware is one of the fastest-growing threats in the Kingdom. Protection requires multiple layers: strong endpoint security, regular backups, network segmentation, employee awareness, and continuous monitoring.
Prime Links helps you deploy the right tools—including AI-based protection and zero-trust controls—to prevent attacks before they spread and ensure recovery without business disruption
Remote and hybrid work introduces risks such as insecure networks, unmanaged devices, and identity theft.
The most effective strategy includes secure VPN or ZTNA, multi-factor authentication, endpoint protection, cloud security, and policy-based access controls.
We design secure remote access frameworks tailored to Saudi compliance requirements, ensuring your team can work safely from anywhere.
Costs depend on the required solutions assessment, SOC services, OT protection, cloud security, etc. We provide scalable options for all business sizes.
Yes. We provide end-to-end implementation, integration, and ongoing support to close all identified gaps.
Yes. We connect customers with leading global vendors to ensure the best technologies and highest level of protection.
Collaborating with industry leaders to deliver world-class solutions







Our Service
Our team is ready to support you with clear guidance, fast responses, and tailored solutions that match your business needs. Whether you want technical details, pricing information, or help choosing the right cybersecurity service, we’re here to make everything simple and transparent.
Contact Us
Our customer service representative helps you to understand what we offer for your business goals.
